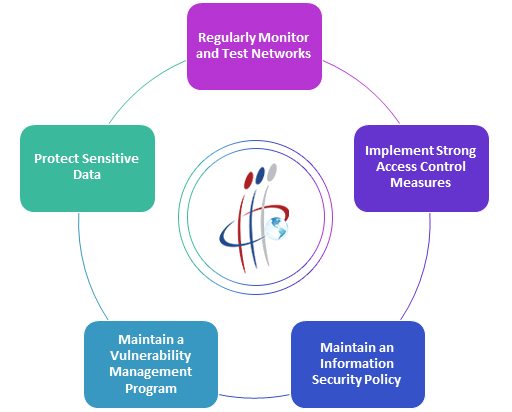
i3intl applies security management procedures including information classification, risk assessment, and risk analysis to identify threats, categorize assets, and rate system which allow us to identify the vulnerabilities and implement effective controls. i3 security management procedures includes many benefits and features such as:
Features:
- Security Program Review
- Standards based GAP Assessments
- Policy and Procedures Development
- Security Awareness Training & Self-Phishing Campaigns
- Manage Compliance & Regulatory Requirements (PCI, SOX, HIPPA)
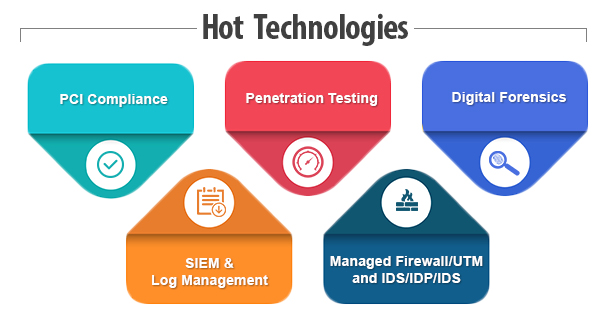
I3 Managed Security Services:
- Professional Security Services – Managed & Monitored Firewall/UTM
- Managed & Monitored IDS/IPS – Log/Security Event Monitoring
- Managed Strong Authentication
Firewall, UTM & IDS/IPS/HIDS Monitoring & Management
Every company needs a disciplined approach to monitoring and managing its security infrastructure. As part of our Managed Security Services, I3intl offers Firewall monitoring and management services.
Features:
- Management, monitoring & incident escalation
- Log collection, reporting & archival
- Security intelligence
- Planning, design & configuration
- Site-to-site & remote access VPN
- Perating costs
- All-in-one capabilities with UTM – FW, IPS, AV, content filtering, VPN
Benefits:
- Augment staff w/access to hard-to-find skills
- Repurpose internal staff on projects more critical to core business
- 24x7x365 monitoring & management
- Manage regulatory & complexity issues associated w/infosec
- Performance-backed SLAs
- Reduced upfront & annual IT operating costs
Log Management and Reporting
Event log management or security information event management (SIEM) is considered an IT best practice, and for regulated industries, an audit compliance requisite. I3intl has you covered with the complexities of log management.
Features:
- Full featured Cloud-Based solution
- Automated Log collection, reporting & archival
- Flexible Data Collection Options
- On-Demand Reporting
- State-of-the-Art Portal, common platform
- Big-Data enabled providing massive scale
Benefits:
- Dramatically reduce the complexity and costs of log management and reporting so you can focus on your core business activities.
- Reduce compliance burden
- Improve security & lower risk
- Easy deployment and unlimited scale

Managed Authentication, Hard and Soft Token
i3 meets regulatory requirements and provide an easy to use, easy to implement, second factor authentication for your remote user access (such as VPN) to critical systems.
Features:
- Fully managed authentication servers hosted at I3intl Security Operations Center
- Hard tokens, SMS, desktop & mobile soft tokens
- Includes integration with customer applications
- 24×7 Service Desk – installation, PIN resets, replacement, application configuration issues, lockouts, change/add/delete modifications
Benefits:
- Low TCO with reduced capex/opex
- Scalability
- Reliability & Performance Guarantees
- Out-of-the-box integration with existing infrastructure
- Reduction in deployment complexity, staffing requirements, administrative and logistics overhead, user management and infrastructure costs
Incident Response, Malware Reverse Engineering
The I3intl incident response executes rapid containment and eradication of threats which minimizes both the duration and impact of a security breach. We can help you prepare for, respond to and recover from even the most complex and large-scale information security incidents.
Features:
- Standards based Incident Response Process development
- Incident Response Process improvements
- Trained Security & Forensic analysts on-demand
- Malware Reverse-engineering and analysis
- Incident Remediation and Root Cause Analysis
Benefits:
- React Faster, React better to unforeseen Information Security Incidents
- Reduce the damage due to an incident, and contain costs
- Recover Faster
How i3 is Different
- All solution are cloud based so no capital cost
- Total ownership of problem and solution
- Easily integrate with current infra setup